A wrapper for the OpenSSL SSL_CTX related functions. More...
#include <SSL_Context.h>
Public Types | |
| enum | { INVALID_METHOD = -1, SSLv2_client = 1, SSLv2_server, SSLv2, SSLv3_client, SSLv3_server, SSLv3, SSLv23_client, SSLv23_server, SSLv23, TLSv1_client, TLSv1_server, TLSv1 } |
Public Member Functions | |
| ACE_SSL_Context (void) | |
| Constructor. | |
| ~ACE_SSL_Context (void) | |
| Destructor. | |
| int | set_mode (int mode=ACE_SSL_Context::SSLv23) |
| int | get_mode (void) const |
| SSL_CTX * | context (void) |
| Get the SSL context. | |
| int | private_key_type (void) const |
| Get the file name and file format used for the private key. | |
| const char * | private_key_file_name (void) const |
| int | private_key (const char *file_name, int type=SSL_FILETYPE_PEM) |
| Set the private key file. | |
| int | verify_private_key (void) |
| Verify that the private key is valid. | |
| int | certificate_type (void) const |
| Get the file name and file format used for the certificate file. | |
| const char * | certificate_file_name (void) const |
| int | certificate (const char *file_name, int type=SSL_FILETYPE_PEM) |
| Set the certificate file. | |
| int | certificate (X509 *cert) |
| Load certificate from memory rather than a file. | |
| int | load_trusted_ca (const char *ca_file=0, const char *ca_dir=0, bool use_env_defaults=true) |
| int | have_trusted_ca (void) const |
| void | set_verify_peer (int strict=0, int once=1, int depth=0) |
| void | default_verify_mode (int mode) |
| int | default_verify_mode (void) const |
| void | default_verify_callback (int(*callback)(int, X509_STORE_CTX *)) |
Diffie-Hellman (DH) Parameters | |
| int | dh_params (const char *file_name, int type=SSL_FILETYPE_PEM) |
| const char * | dh_params_file_name () const |
| int | dh_params_file_type () const |
Static Public Member Functions | |
| static ACE_SSL_Context * | instance (void) |
| static void | report_error (unsigned long error_code) |
| Print SSL error corresponding to the given error code. | |
| static void | report_error (void) |
| Print the last SSL error for the current thread. | |
OpenSSL Random Number Generator Seed Related Methods | |
| static int | random_seed (const char *seed) |
| static int | egd_file (const char *socket_file) |
| static int | seed_file (const char *seed_file, long bytes=-1) |
Public Attributes | |
| int(*)(int, X509_STORE_CTX *) | default_verify_callback (void) const |
Private Member Functions | |
| void | check_context (void) |
| Verify if the context has been initialized or not. | |
| void | ssl_library_init () |
| @ More to document | |
| void | ssl_library_fini () |
| ACE_SSL_Context (const ACE_SSL_Context &) | |
| ACE_SSL_Context & | operator= (const ACE_SSL_Context &) |
Private Attributes | |
| SSL_CTX * | context_ |
| The SSL_CTX structure. | |
| int | mode_ |
| Cache the mode so we can answer fast. | |
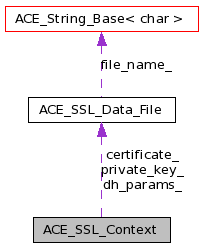
| ACE_SSL_Data_File | private_key_ |
| The private key, certificate, and Diffie-Hellman parameters files. | |
| ACE_SSL_Data_File | certificate_ |
| ACE_SSL_Data_File | dh_params_ |
| int | default_verify_mode_ |
| The default verify mode. | |
| int(* | default_verify_callback_ )(int, X509_STORE_CTX *) |
| The default verify callback. | |
| int | have_ca_ |
| count of successful CA load attempts | |
A wrapper for the OpenSSL SSL_CTX related functions.
This class provides a wrapper for the SSL_CTX data structure. Since most applications have a single SSL_CTX structure, this class can be used as a singleton.
Definition at line 75 of file SSL_Context.h.
| anonymous enum |
| INVALID_METHOD | |
| SSLv2_client | |
| SSLv2_server | |
| SSLv2 | |
| SSLv3_client | |
| SSLv3_server | |
| SSLv3 | |
| SSLv23_client | |
| SSLv23_server | |
| SSLv23 | |
| TLSv1_client | |
| TLSv1_server | |
| TLSv1 |
Definition at line 83 of file SSL_Context.h.
{
INVALID_METHOD = -1,
SSLv2_client = 1,
SSLv2_server,
SSLv2,
SSLv3_client,
SSLv3_server,
SSLv3,
SSLv23_client,
SSLv23_server,
SSLv23,
TLSv1_client,
TLSv1_server,
TLSv1
};
| ACE_SSL_Context::ACE_SSL_Context | ( | void | ) |
Constructor.
Definition at line 111 of file SSL_Context.cpp.
: context_ (0), mode_ (-1), default_verify_mode_ (SSL_VERIFY_NONE), default_verify_callback_ (0), have_ca_ (0) { ACE_SSL_Context::ssl_library_init (); }
| ACE_SSL_Context::~ACE_SSL_Context | ( | void | ) |
Destructor.
Definition at line 121 of file SSL_Context.cpp.
{
if (this->context_)
{
::SSL_CTX_free (this->context_);
this->context_ = 0;
}
ACE_SSL_Context::ssl_library_fini ();
}
| ACE_SSL_Context::ACE_SSL_Context | ( | const ACE_SSL_Context & | ) | [private] |
| int ACE_SSL_Context::certificate | ( | const char * | file_name, | |
| int | type = SSL_FILETYPE_PEM | |||
| ) |
Set the certificate file.
Definition at line 456 of file SSL_Context.cpp.
{
if (this->certificate_.type () != -1)
return 0;
this->certificate_ = ACE_SSL_Data_File (file_name, type);
this->check_context ();
if (::SSL_CTX_use_certificate_file (this->context_,
this->certificate_.file_name (),
this->certificate_.type ()) <= 0)
{
this->certificate_ = ACE_SSL_Data_File ();
return -1;
}
else
return 0;
}
| int ACE_SSL_Context::certificate | ( | X509 * | cert | ) |
Load certificate from memory rather than a file.
Definition at line 478 of file SSL_Context.cpp.
{
// Is it really a good idea to return 0 if we're not setting the
// certificate?
if (this->certificate_.type () != -1)
return 0;
this->check_context();
if (::SSL_CTX_use_certificate (this->context_, cert) <= 0)
{
return -1;
}
else
{
// No file is associated with the certificate, set this to a fictional
// value so we don't reset it later.
this->certificate_ = ACE_SSL_Data_File ("MEMORY CERTIFICATE");
return 0;
}
}
| const char * ACE_SSL_Context::certificate_file_name | ( | void | ) | const |
Definition at line 73 of file SSL_Context.inl.
{
return this->certificate_.file_name ();
}
| int ACE_SSL_Context::certificate_type | ( | void | ) | const |
Get the file name and file format used for the certificate file.
Definition at line 67 of file SSL_Context.inl.
{
return this->certificate_.type ();
}
| void ACE_SSL_Context::check_context | ( | void | ) | [private] |
Verify if the context has been initialized or not.
Definition at line 36 of file SSL_Context.inl.
{
if (this->context_ == 0)
{
this->set_mode ();
}
::SSL_CTX_set_verify (this->context_, this->default_verify_mode (),
this->default_verify_callback ());
}
| SSL_CTX * ACE_SSL_Context::context | ( | void | ) |
Get the SSL context.
Definition at line 48 of file SSL_Context.inl.
{
this->check_context ();
return this->context_;
}
| void ACE_SSL_Context::default_verify_callback | ( | int(*)(int, X509_STORE_CTX *) | callback | ) |
Set and query the default verify callback for this context, it is inherited by all the ACE_SSL objects created using the context. It can be overriden on a per-ACE_SSL object.
| int ACE_SSL_Context::default_verify_mode | ( | void | ) | const |
Definition at line 97 of file SSL_Context.inl.
{
return this->default_verify_mode_;
}
| void ACE_SSL_Context::default_verify_mode | ( | int | mode | ) |
TODO: a implementation that will lookup the CTX table for the list of files and paths etc. Query the location of trusted certification authority certificates. Set and query the default verify mode for this context, it is inherited by all the ACE_SSL objects created using the context. It can be overriden on a per-ACE_SSL object.
Definition at line 91 of file SSL_Context.inl.
{
this->default_verify_mode_ = mode;
}
| int ACE_SSL_Context::dh_params | ( | const char * | file_name, | |
| int | type = SSL_FILETYPE_PEM | |||
| ) |
Load Diffie-Hellman parameters from file_name. The specified file can be a standalone file containing only DH parameters (e.g., as created by openssl dhparam), or it can be a certificate which has a PEM-encoded set of DH params concatenated on to i.
Definition at line 603 of file SSL_Context.cpp.
{
if (this->dh_params_.type () != -1)
return 0;
// For now we only support PEM encodings
if (type != SSL_FILETYPE_PEM)
return -1;
this->dh_params_ = ACE_SSL_Data_File (file_name, type);
this->check_context ();
{
// Swiped from Rescorla's examples and the OpenSSL s_server.c app
DH * ret=0;
BIO * bio = 0;
if ((bio = ::BIO_new_file (this->dh_params_.file_name (), "r")) == 0)
{
this->dh_params_ = ACE_SSL_Data_File ();
return -1;
}
ret = PEM_read_bio_DHparams (bio, 0, 0, 0);
BIO_free (bio);
if (ret == 0)
{
this->dh_params_ = ACE_SSL_Data_File ();
return -1;
}
if (::SSL_CTX_set_tmp_dh (this->context_, ret) < 0)
{
this->dh_params_ = ACE_SSL_Data_File ();
return -1;
}
DH_free (ret);
}
return 0;
}
| const char * ACE_SSL_Context::dh_params_file_name | ( | void | ) | const |
Load Diffie-Hellman parameters from file_name. The specified file can be a standalone file containing only DH parameters (e.g., as created by openssl dhparam), or it can be a certificate which has a PEM-encoded set of DH params concatenated on to i.
Definition at line 85 of file SSL_Context.inl.
{
return this->dh_params_.file_name ();
}
| int ACE_SSL_Context::dh_params_file_type | ( | void | ) | const |
Load Diffie-Hellman parameters from file_name. The specified file can be a standalone file containing only DH parameters (e.g., as created by openssl dhparam), or it can be a certificate which has a PEM-encoded set of DH params concatenated on to i.
Definition at line 79 of file SSL_Context.inl.
{
return this->dh_params_.type ();
}
| int ACE_SSL_Context::egd_file | ( | const char * | socket_file | ) | [static] |
Set the Entropy Gathering Daemon (EGD) UNIX domain socket file to read random seed values from.
Definition at line 539 of file SSL_Context.cpp.
{
#if OPENSSL_VERSION_NUMBER < 0x00905100L
// OpenSSL < 0.9.5 doesn't have EGD support.
ACE_UNUSED_ARG (socket_file);
ACE_NOTSUP_RETURN (-1);
#else
// RAND_egd() returns the amount of entropy used to seed the random
// number generator. The actual value should be greater than 16,
// i.e. 128 bits.
if (::RAND_egd (socket_file) > 0)
return 0;
else
return -1;
#endif /* OPENSSL_VERSION_NUMBER >= 0x00905100L */
}
| int ACE_SSL_Context::get_mode | ( | void | ) | const |
Definition at line 114 of file SSL_Context.inl.
{
return this->mode_;
}
| int ACE_SSL_Context::have_trusted_ca | ( | void | ) | const |
Test whether any CA locations have been successfully loaded and return the number of successful attempts.
| >0 | The number of successful CA load attempts. | |
| 0 | If all CA load attempts have failed. |
Definition at line 120 of file SSL_Context.inl.
{
return this->have_ca_;
}
| ACE_SSL_Context * ACE_SSL_Context::instance | ( | void | ) | [static] |
The Singleton context, the SSL components use the singleton if nothing else is available.
Definition at line 133 of file SSL_Context.cpp.
| int ACE_SSL_Context::load_trusted_ca | ( | const char * | ca_file = 0, |
|
| const char * | ca_dir = 0, |
|||
| bool | use_env_defaults = true | |||
| ) |
Load the location of the trusted certification authority certificates. Note that CA certificates are stored in PEM format as a sequence of certificates in ca_file or as a set of individual certificates in ca_dir (or both).
Note this method is called by set_mode() to load the default environment settings for ca_file and ca_dir, if any. This allows for automatic service configuration (and backward compatibility with previous versions).
Note that the underlying SSL function will add valid file and directory names to the load location lists maintained as part of the SSL_CTX table. It therefore doesn't make sense to keep a copy of the file and path name of the most recently added ca_file or ca_path.
| [in] | ca_file | CA file pathname. Passed to SSL_CTX_load_verify_locations() if not 0. If 0, behavior depends on the value of use_env_defaults. |
| [in] | ca_dir | CA directory pathname. Passed to SSL_CTX_load_verify_locations() if not 0. If 0, behavior depends on the value of use_env_defaults. |
| [in] | use_env_defaults | If false, the specified ca_file argument is passed to SSL_CTX_load_verify_locations(), regardless of its value. If true (the default), additional defaults can be applied to either ca_file, ca_dir, or both. The following additional defaults are applied when the ca_file argument is 0:
|
Definition at line 306 of file SSL_Context.cpp.
{
this->check_context ();
if (ca_file == 0 && use_env_defaults)
{
// Use the default environment settings.
ca_file = ACE_OS::getenv (ACE_SSL_CERT_FILE_ENV);
#ifdef ACE_DEFAULT_SSL_CERT_FILE
if (ca_file == 0)
ca_file = ACE_DEFAULT_SSL_CERT_FILE;
#endif
}
if (ca_dir == 0 && use_env_defaults)
{
// Use the default environment settings.
ca_dir = ACE_OS::getenv (ACE_SSL_CERT_DIR_ENV);
#ifdef ACE_DEFAULT_SSL_CERT_DIR
if (ca_dir == 0)
ca_dir = ACE_DEFAULT_SSL_CERT_DIR;
#endif
}
// NOTE: SSL_CTX_load_verify_locations() returns 0 on error.
if (::SSL_CTX_load_verify_locations (this->context_,
ca_file,
ca_dir) <= 0)
{
if (ACE::debug ())
ACE_SSL_Context::report_error ();
return -1;
}
++this->have_ca_;
// For TLS/SSL servers scan all certificates in ca_file and ca_dir and
// list them as acceptable CAs when requesting a client certificate.
if (mode_ == SSLv23
|| mode_ == SSLv23_server
|| mode_ == TLSv1
|| mode_ == TLSv1_server
|| mode_ == SSLv3
|| mode_ == SSLv3_server
|| mode_ == SSLv2
|| mode_ == SSLv2_server)
{
// Note: The STACK_OF(X509_NAME) pointer is a copy of the pointer in
// the CTX; any changes to it by way of these function calls will
// change the CTX directly.
STACK_OF (X509_NAME) * cert_names = 0;
cert_names = ::SSL_CTX_get_client_CA_list (this->context_);
bool error = false;
// Add CAs from both the file and dir, if specified. There should
// already be a STACK_OF(X509_NAME) in the CTX, but if not, we create
// one.
if (ca_file)
{
if (cert_names == 0)
{
if ((cert_names = ::SSL_load_client_CA_file (ca_file)) != 0)
::SSL_CTX_set_client_CA_list (this->context_, cert_names);
else
error = true;
}
else
{
// Add new certificate names to the list.
error = (0 == ::SSL_add_file_cert_subjects_to_stack (cert_names,
ca_file));
}
if (error)
{
if (ACE::debug ())
ACE_SSL_Context::report_error ();
return -1;
}
}
// SSL_add_dir_cert_subjects_to_stack is defined at 0.9.8a (but not
// on OpenVMS or Mac Classic); it may be available earlier. Change
// this comparison if so.
#if defined (OPENSSL_VERSION_NUMBER) && (OPENSSL_VERSION_NUMBER >= 0x0090801fL)
# if !defined (OPENSSL_SYS_VMS) && !defined (OPENSSL_SYS_MACINTOSH_CLASSIC)
# if !defined (OPENSSL_SYS_WIN32) || (OPENSSL_VERSION_NUMBER > 0x0090807fL)
if (ca_dir != 0)
{
if (cert_names == 0)
{
if ((cert_names = sk_X509_NAME_new_null ()) == 0)
{
if (ACE::debug ())
ACE_SSL_Context::report_error ();
return -1;
}
::SSL_CTX_set_client_CA_list (this->context_, cert_names);
}
if (0 == ::SSL_add_dir_cert_subjects_to_stack (cert_names, ca_dir))
{
if (ACE::debug ())
ACE_SSL_Context::report_error ();
return -1;
}
}
# endif /* !OPENSSL_SYS_WIN32 || OPENSSL_VERSION_NUMBER >= 0x0090807fL */
# endif /* !OPENSSL_SYS_VMS && !OPENSSL_SYS_MACINTOSH_CLASSIC */
#endif /* OPENSSL_VERSION_NUMBER >= 0.9.8a release */
}
return 0;
}
| ACE_SSL_Context& ACE_SSL_Context::operator= | ( | const ACE_SSL_Context & | ) | [private] |
| int ACE_SSL_Context::private_key | ( | const char * | file_name, | |
| int | type = SSL_FILETYPE_PEM | |||
| ) |
Set the private key file.
Definition at line 426 of file SSL_Context.cpp.
{
if (this->private_key_.type () != -1)
return 0;
this->check_context ();
this->private_key_ = ACE_SSL_Data_File (file_name, type);
if (::SSL_CTX_use_PrivateKey_file (this->context_,
this->private_key_.file_name (),
this->private_key_.type ()) <= 0)
{
this->private_key_ = ACE_SSL_Data_File ();
return -1;
}
else
return this->verify_private_key ();
}
| const char * ACE_SSL_Context::private_key_file_name | ( | void | ) | const |
Definition at line 61 of file SSL_Context.inl.
{
return this->private_key_.file_name ();
}
| int ACE_SSL_Context::private_key_type | ( | void | ) | const |
Get the file name and file format used for the private key.
Definition at line 55 of file SSL_Context.inl.
{
return this->private_key_.type ();
}
| int ACE_SSL_Context::random_seed | ( | const char * | seed | ) | [static] |
Seed the underlying random number generator. This value should have at least 128 bits of entropy.
Definition at line 525 of file SSL_Context.cpp.
{
int len = ACE_Utils::truncate_cast<int> (ACE_OS::strlen (seed));
::RAND_seed (seed, len);
#if OPENSSL_VERSION_NUMBER >= 0x00905100L
// RAND_status() returns 1 if the PRNG has enough entropy.
return (::RAND_status () == 1 ? 0 : -1);
#else
return 0; // Ugly, but OpenSSL <= 0.9.4 doesn't have RAND_status().
#endif /* OPENSSL_VERSION_NUMBER >= 0x00905100L */
}
| void ACE_SSL_Context::report_error | ( | unsigned long | error_code | ) | [static] |
Print SSL error corresponding to the given error code.
Definition at line 574 of file SSL_Context.cpp.
{
if (error_code == 0)
return;
char error_string[256];
// OpenSSL < 0.9.6a doesn't have ERR_error_string_n() function.
#if OPENSSL_VERSION_NUMBER >= 0x0090601fL
(void) ::ERR_error_string_n (error_code, error_string, sizeof error_string);
#else /* OPENSSL_VERSION_NUMBER >= 0x0090601fL */
(void) ::ERR_error_string (error_code, error_string);
#endif /* OPENSSL_VERSION_NUMBER >= 0x0090601fL */
ACE_ERROR ((LM_ERROR,
ACE_TEXT ("ACE_SSL (%P|%t) error code: %u - %C\n"),
error_code,
error_string));
}
| void ACE_SSL_Context::report_error | ( | void | ) | [static] |
Print the last SSL error for the current thread.
Definition at line 595 of file SSL_Context.cpp.
{
unsigned long err = ::ERR_get_error ();
ACE_SSL_Context::report_error (err);
ACE_OS::last_error (err);
}
| int ACE_SSL_Context::seed_file | ( | const char * | seed_file, | |
| long | bytes = -1 | |||
| ) | [static] |
Set the file that contains the random seed value state, and the amount of bytes to read. "-1" bytes causes the entire file to be read.
Definition at line 557 of file SSL_Context.cpp.
{
// RAND_load_file() returns the number of bytes used to seed the
// random number generator. If the file reads ok, check RAND_status to
// see if it got enough entropy.
if (::RAND_load_file (seed_file, bytes) > 0)
#if OPENSSL_VERSION_NUMBER >= 0x00905100L
// RAND_status() returns 1 if the PRNG has enough entropy.
return (::RAND_status () == 1 ? 0 : -1);
#else
return 0; // Ugly, but OpenSSL <= 0.9.4 doesn't have RAND_status().
#endif /* OPENSSL_VERSION_NUMBER >= 0x00905100L */
else
return -1;
}
| int ACE_SSL_Context::set_mode | ( | int | mode = ACE_SSL_Context::SSLv23 |
) |
Set the CTX mode. The mode can be set only once, afterwards the function has no effect and returns -1. Once the mode is set the underlying SSL_CTX is initialized and the class can be used. If the mode is not set, then the class automatically initializes itself to the default mode.
Definition at line 229 of file SSL_Context.cpp.
{
ACE_MT (ACE_GUARD_RETURN (ACE_Recursive_Thread_Mutex,
ace_ssl_mon,
*ACE_Static_Object_Lock::instance (),
-1));
if (this->context_ != 0)
return -1;
#if OPENSSL_VERSION_NUMBER >= 0x10000002
const SSL_METHOD *method = 0;
#else
SSL_METHOD *method = 0;
#endif
switch (mode)
{
case ACE_SSL_Context::SSLv2_client:
method = ::SSLv2_client_method ();
break;
case ACE_SSL_Context::SSLv2_server:
method = ::SSLv2_server_method ();
break;
case ACE_SSL_Context::SSLv2:
method = ::SSLv2_method ();
break;
case ACE_SSL_Context::SSLv3_client:
method = ::SSLv3_client_method ();
break;
case ACE_SSL_Context::SSLv3_server:
method = ::SSLv3_server_method ();
break;
case ACE_SSL_Context::SSLv3:
method = ::SSLv3_method ();
break;
case ACE_SSL_Context::SSLv23_client:
method = ::SSLv23_client_method ();
break;
case ACE_SSL_Context::SSLv23_server:
method = ::SSLv23_server_method ();
break;
case ACE_SSL_Context::SSLv23:
method = ::SSLv23_method ();
break;
case ACE_SSL_Context::TLSv1_client:
method = ::TLSv1_client_method ();
break;
case ACE_SSL_Context::TLSv1_server:
method = ::TLSv1_server_method ();
break;
case ACE_SSL_Context::TLSv1:
method = ::TLSv1_method ();
break;
default:
method = ::SSLv3_method ();
break;
}
this->context_ = ::SSL_CTX_new (method);
if (this->context_ == 0)
return -1;
this->mode_ = mode;
// Load the trusted certificate authority (default) certificate
// locations. But do not return -1 on error, doing so confuses CTX
// allocation (severe error) with the less important loading of CA
// certificate location error. If it is important for your
// application then call ACE_SSL_Context::have_trusted_ca(),
// immediately following this call to set_mode().
(void) this->load_trusted_ca ();
return 0;
}
| void ACE_SSL_Context::set_verify_peer | ( | int | strict = 0, |
|
| int | once = 1, |
|||
| int | depth = 0 | |||
| ) |
Use this method when certificate chain verification is required. The default server behaviour is SSL_VERIFY_NONE i.e. client certicates are requested for verified. This method can be used to configure server to request client certificates and perform the certificate verification. If <strict> is set true the client connection is rejected when certificate verification fails. Otherwise the session is accepted with a warning, which is the default behaviour. If <once> is set true (default), certificates are requested only once per session. The last parameter <depth> can be used to set the verification depth.
Note for verification to work correctly there should be a valid CA name list set using load_trusted_ca().
Note that this method overrides the use of the default_verify_mode() method.
Definition at line 502 of file SSL_Context.cpp.
{
this->check_context ();
// Setup the peer verififcation mode.
int verify_mode = SSL_VERIFY_PEER;
if (once)
verify_mode |= SSL_VERIFY_CLIENT_ONCE;
if (strict)
verify_mode |= SSL_VERIFY_FAIL_IF_NO_PEER_CERT;
// set the default verify mode
this->default_verify_mode (verify_mode);
// Set the max certificate depth but later let the verify_callback
// catch the depth error by adding one to the required depth.
if (depth > 0)
::SSL_CTX_set_verify_depth (this->context_, depth + 1);
}
| void ACE_SSL_Context::ssl_library_fini | ( | void | ) | [private] |
Definition at line 200 of file SSL_Context.cpp.
{
ACE_MT (ACE_GUARD (ACE_Recursive_Thread_Mutex,
ace_ssl_mon,
*ACE_Static_Object_Lock::instance ()));
--ssl_library_init_count;
if (ssl_library_init_count == 0)
{
// Explicitly close the singleton
ACE_Unmanaged_Singleton<ACE_SSL_Context, ACE_SYNCH_MUTEX>::close();
::ERR_free_strings ();
::EVP_cleanup ();
// Clean up the locking callbacks after everything else has been
// cleaned up.
#ifdef ACE_HAS_THREADS
::CRYPTO_set_locking_callback (0);
ssl_locks = 0;
delete [] this->locks_;
this->locks_ = 0;
#endif /* ACE_HAS_THREADS */
}
}
| void ACE_SSL_Context::ssl_library_init | ( | void | ) | [private] |
@ More to document
Definition at line 139 of file SSL_Context.cpp.
{
ACE_MT (ACE_GUARD (ACE_Recursive_Thread_Mutex,
ace_ssl_mon,
*ACE_Static_Object_Lock::instance ()));
if (ssl_library_init_count == 0)
{
// Initialize the locking callbacks before initializing anything
// else.
#ifdef ACE_HAS_THREADS
int const num_locks = ::CRYPTO_num_locks ();
this->locks_ = new lock_type[num_locks];
ssl_locks = this->locks_;
# if !defined (WIN32)
// This call isn't necessary on some platforms. See the CRYPTO
// library's threads(3) man page for details.
::CRYPTO_set_id_callback (ACE_SSL_THREAD_ID_NAME);
# endif /* !WIN32 */
::CRYPTO_set_locking_callback (ACE_SSL_LOCKING_CALLBACK_NAME);
#endif /* ACE_HAS_THREADS */
::SSLeay_add_ssl_algorithms ();
::SSL_load_error_strings ();
// Seed the random number generator. Note that the random
// number generator can be seeded more than once to "stir" its
// state.
#ifdef WIN32
// Seed the random number generator by sampling the screen.
::RAND_screen ();
#endif /* WIN32 */
#if OPENSSL_VERSION_NUMBER >= 0x00905100L
// OpenSSL < 0.9.5 doesn't have EGD support.
const char *egd_socket_file =
ACE_OS::getenv (ACE_SSL_EGD_FILE_ENV);
if (egd_socket_file != 0)
(void) this->egd_file (egd_socket_file);
#endif /* OPENSSL_VERSION_NUMBER */
const char *rand_file = ACE_OS::getenv (ACE_SSL_RAND_FILE_ENV);
if (rand_file != 0)
{
(void) this->seed_file (rand_file);
}
// Initialize the mutexes that will be used by the SSL and
// crypto library.
}
++ssl_library_init_count;
}
| int ACE_SSL_Context::verify_private_key | ( | void | ) |
Verify that the private key is valid.
Definition at line 448 of file SSL_Context.cpp.
{
this->check_context ();
return (::SSL_CTX_check_private_key (this->context_) <= 0 ? -1 : 0);
}
Definition at line 366 of file SSL_Context.h.
SSL_CTX* ACE_SSL_Context::context_ [private] |
The SSL_CTX structure.
Definition at line 359 of file SSL_Context.h.
Definition at line 288 of file SSL_Context.h.
int(* ACE_SSL_Context::default_verify_callback_)(int, X509_STORE_CTX *) [private] |
The default verify callback.
Definition at line 373 of file SSL_Context.h.
int ACE_SSL_Context::default_verify_mode_ [private] |
The default verify mode.
Definition at line 370 of file SSL_Context.h.
ACE_SSL_Data_File ACE_SSL_Context::dh_params_ [private] |
Definition at line 367 of file SSL_Context.h.
int ACE_SSL_Context::have_ca_ [private] |
count of successful CA load attempts
Definition at line 376 of file SSL_Context.h.
int ACE_SSL_Context::mode_ [private] |
Cache the mode so we can answer fast.
Definition at line 362 of file SSL_Context.h.
The private key, certificate, and Diffie-Hellman parameters files.
Definition at line 365 of file SSL_Context.h.
 1.7.0
1.7.0